It is one of the most terrifying moments for a non-technical founder or business leader.
Your lead developer, the person who built your entire software platform from scratch, just put in their two weeks' notice. Or worse, they have already walked out the door.
Suddenly, you realise the horrific truth: nobody else in the company actually knows how the software works. There is no technical documentation. The server passwords are saved on their personal laptop. The entire architecture of your business exists solely in the brain of someone who no longer works for you.
Your company's most valuable asset is now a "Ghost Ship." The engine is running, and the ship is moving, but there is absolutely no one at the steering wheel. If it hits a wave (a server crash or a bug), you have no way to fix it.
The Executive Summary: In software engineering, this is known as a Bus Factor of 1 (meaning if one person gets hit by a bus, the project dies). If you find yourself holding the keys to a ghost ship codebase, do not panic, and do not immediately hire a cheap freelancer to start blindly pushing new code. Your immediate priority is securing the perimeter. You must lock down administrative access, freeze all new feature development, and bring in a specialised software agency to conduct a forensic Technical Code Audit.
Here is the exact, step-by-step triage plan to secure your intellectual property and safely transition your software to a new team.
Step 1: Secure the Perimeter (The 24-Hour Lockdown)
Before the developer leaves, or the moment you realise they are gone, you must legally and digitally secure your assets. An upset or disorganised former employee retaining administrative access to your cloud infrastructure is a massive security and compliance liability.
You (or a trusted executive) must verify "Owner" or "Super Admin" access to the following four critical systems immediately:
- The Source Code Repository: This is where your actual code lives. Verify you own the master account for GitHub, GitLab, or Bitbucket.
- Cloud Infrastructure & Hosting: Ensure the company credit card is on file and you have master access to AWS, Microsoft Azure, Google Cloud, or DigitalOcean.
- Domain & DNS Registrars: GoDaddy, Cloudflare, Namecheap. If your domain expires or is maliciously rerouted, your entire app goes offline.
- Third-Party APIs and Gateways: Secure the master logins for Stripe (payments), Twilio (SMS), SendGrid (emails), and your Apple/Google App Store Developer accounts.
Revoke Access: Once you have verified you hold the master keys, permanently revoke the departing developer's access to all systems, Slack channels, and internal VPNs.
Step 2: The "Code Freeze" (Do Not Touch Anything)
When a lead developer quits, business leaders often panic because they promised clients a new feature by the end of the month. They rush to Upwork, hire a discount freelance developer, and tell them to "finish the feature."
This is the fastest way to break your software.
Undocumented code written by a single "lone wolf" developer is incredibly fragile. It is usually full of strange workarounds and hardcoded rules. If a new developer blindly injects new code into a system they don't understand, they will trigger a cascade of fatal bugs that take the entire platform offline.
You must institute a strict Code Freeze. Communicate to your stakeholders that all new feature development is paused for 30 days. The only code that should be written during this period is emergency bug fixes. The singular goal right now is stability.
Step 3: Bring in the "Paramedics" (The Forensic Code Audit)
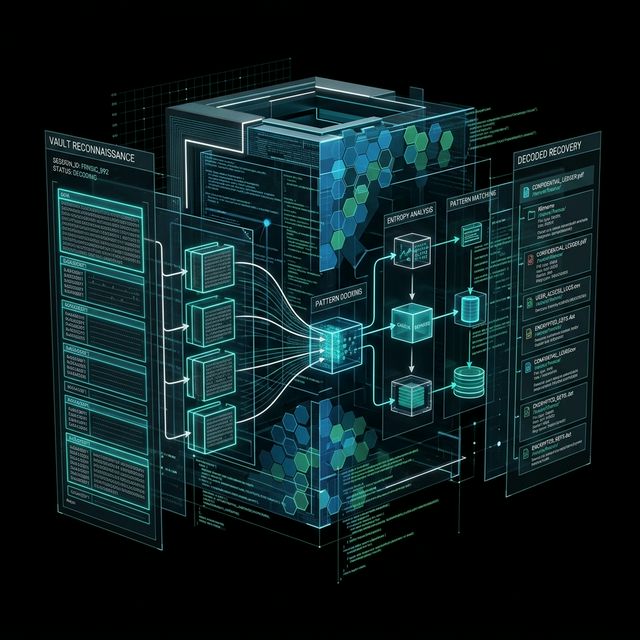
You cannot manage what you do not understand. To take over a Ghost Ship, you need an experienced external team to reverse-engineer the code.
At Redi Software, we specialise in Legacy Code Takeovers. When we step into a Ghost Ship scenario, our senior software architects perform a rapid, deep-dive Technical Code Audit. We act as software forensic scientists to answer three critical questions for the CEO:
- Is the code secure? Are there glaring vulnerabilities, exposed API keys, or compliance violations (HIPAA, SOC 2, GDPR) that the previous developer hid?
- Where are the structural cracks? Did they use modern, supported frameworks (like React, Python, or Node.js), or is the application built on outdated, unsupported "spaghetti code" that is about to collapse?
- How do we keep the lights on? We map out the deployment pipeline. If the server crashes at 2:00 AM, we document the exact step-by-step process required to reboot the system and restore the database backups.
At the end of the audit, we hand the CEO a plain-English diagnostic report. You will finally know exactly what you own, how healthy it is, and what it will cost to maintain.
Step 4: Curing the "Bus Factor" Permanently
The ultimate goal of taking over a Ghost Ship isn't just to keep it floating; it is to ensure your company is never held hostage by a single employee again.
Relying on one brilliant but disorganised developer is a massive business risk. When you transition your software to a professional custom development agency, you are buying institutional stability.
- Forced Documentation: We do not allow code to be merged unless it is heavily commented and documented in a central company wiki.
- Automated Testing: We build automated safety nets. If a new developer accidentally writes bad code, the automated tests catch it and block the deployment before it ever reaches your customers.
- The Agency Redundancy: When you partner with us, you aren't hiring one person. You get an entire team of architects, frontend developers, backend engineers, and QA testers. If one of our engineers goes on holiday or leaves, another one steps in seamlessly. Your business never skips a beat.
The 72-Hour Rescue Mission
The Problem: A mid-market SaaS company processing $2M in annual recurring revenue was plunged into crisis when their founding CTO left abruptly due to a dispute. There was zero documentation, the AWS server architecture was a tangled mess, and the platform was scheduled for a massive enterprise client onboarding in two weeks.
The Solution: Redi Software was brought in for an emergency takeover. Within 72 hours, we legally secured all 14 of their fragmented cloud accounts, executed a code freeze, and reverse-engineered the core database architecture.
The ROI: We successfully mapped the undocumented API integrations and implemented a secure CI/CD (Continuous Integration and Continuous Deployment) pipeline. The enterprise onboarding went off flawlessly. We now act as their dedicated, outsourced engineering team, completely eliminating their "Bus Factor" risk while saving them $60,000 a year in internal hiring costs.
Free Lead Magnet: The Emergency Code Takeover Checklist
Has your developer just given their notice? Do not let them leave the building until you have completed this list. Download our free Emergency Code Takeover Checklist. It contains the 15 exact questions you must ask, the passwords you must secure, and the cloud assets you must legally transfer to protect your intellectual property today.
The Bottom Line
When your lead developer leaves, it feels like a crisis. But it is actually a massive opportunity to mature your business. It is the catalyst that forces you to upgrade from a fragile, "lone wolf" startup mentality to a secure, documented, enterprise-grade engineering culture.
Do not let your company's most valuable intellectual property remain a mystery. By securing your assets, freezing deployments, and bringing in a team of professional software architects to audit the damage, you can take the wheel of the ghost ship and steer it back to safety.
Are you currently holding a codebase you don't understand?
At Redi Software, we specialise in high-stakes code rescues and legacy system takeovers. Book a Confidential Triage Consultation today. We will sign an NDA, review your current situation, and give you an immediate, objective action plan to secure your software and restore your peace of mind.
BOOK YOUR CONFIDENTIAL RESCUE CONSULTATION TODAYFrequently Asked Questions (FAQ)
What does "Bus Factor" mean in business?
The "Bus Factor" (or Truck Factor) is a risk management concept. It asks: How many key team members would need to be hit by a bus before the project or business completely collapses? If all the technical knowledge, passwords, and architecture of your software exist in only one developer's head, your Bus Factor is 1. A mature software company mitigates this risk through rigorous documentation and team cross-training, pushing the Bus Factor as high as possible.
Can another developer actually understand undocumented code?
Yes, but it requires highly experienced senior engineers. Junior developers will look at undocumented code and immediately declare it needs to be "rewritten from scratch" because they don't know how to read it. Senior software architects use specialised diagnostic tools to trace the database logic, map the API calls, and reverse-engineer the business rules to figure out exactly what the previous developer was doing.
Who legally owns the code if a freelance developer quits?
This depends entirely on your contract. If you signed a standard Master Services Agreement (MSA) or an employment contract with an "Intellectual Property Assignment" clause, the company owns the code. If you hired a freelancer on a handshake deal without a contract, they may legally hold the copyright to the code they wrote. You must consult a legal professional immediately to ensure the departing developer signs an IP transfer agreement before they leave.
How much does a Forensic Code Audit cost?
An independent Technical Code Audit typically ranges from $5,000 to $15,000 depending on the size and complexity of the application. It is the most critical investment a CEO can make during a technical transition. Attempting to build on top of an undocumented, messy codebase without mapping it first will inevitably lead to catastrophic system failures and tens of thousands of dollars in wasted development time.